
Veteran-Owned Cybersecurity Consultancy
Securing operations without disrupting them.
ICS, SCADA, and OT security assessments, penetration testing, open-source tooling, and SANS training for organizations that operate critical infrastructure.
Where To Start
How Can We Help?
Whether you're a student, a practitioner, or an organization looking for assessment services -- here's how to find what you need.
Learn
Training, mentoring, and course resources for students and practitioners entering ICS/OT cybersecurity.
Use Our Tools
Free, open-source projects for ICS/OT security assessments, hardening, and research.
Work With Us
Security assessments, penetration testing, and research for industrial environments.
Our Expertise
Security Skills
Four disciplines that define our approach to securing industrial environments.
Aggressors
We look at your technology the way adversaries do, searching for the unintended uses, the overlooked paths, and the creative misuse of what was built for another purpose. We do not design industrial processes, but we know how to find the paths through them that others would exploit. Authorized penetration testing and bench testing, conducted with the discipline an ICS/OT environment requires.
Defenders
We help teams prevent, detect, respond, and recover cost-effectively, in ways that fit how your operations actually run. Our offensive work feeds directly into stronger defenses. We focus on implementation issues rather than vulnerabilities, because the devices and solutions in your environment were chosen for a reason. And we threat hunt, looking for what adversaries may already be doing, to shrink the gap between detection, response, and protecting operations.
Researchers
We pull apart devices, protocols, and technologies to understand how they actually work. What we learn goes back to clients, vendors, and the broader community so people can see what they know about their environments, and what they do not. The goal is better decisions across every phase of operations. Many vendors, and too many integrators, miss the minute technical details that have the biggest impact on operational risk. We help teams find and address those details.
Instructors
Knowledge spreads beyond the classroom. Teaching ICS/OT cybersecurity concepts around the world makes industries stronger, makes threat actors' work harder, and prepares the next wave of practitioners to carry the torch. We contribute through SANS courses, workshops, open source projects, conference presentations, and volunteering with non-profit organizations.
Recent
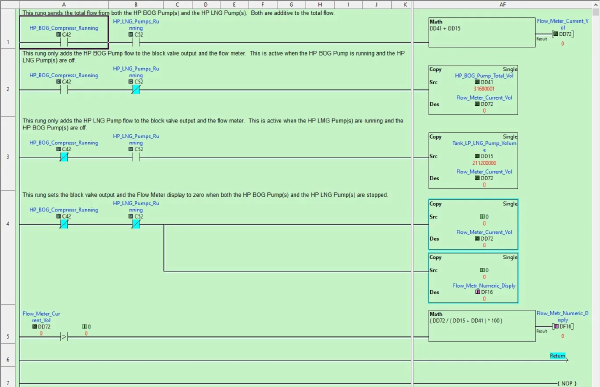
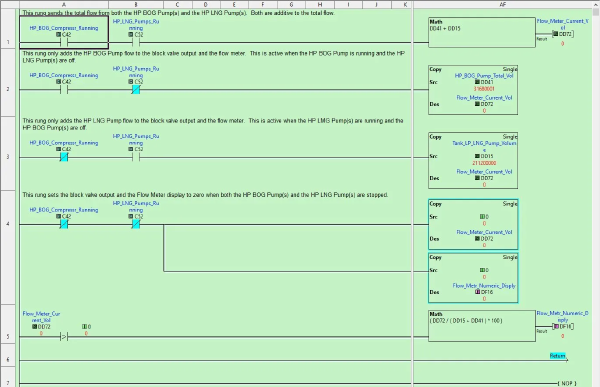
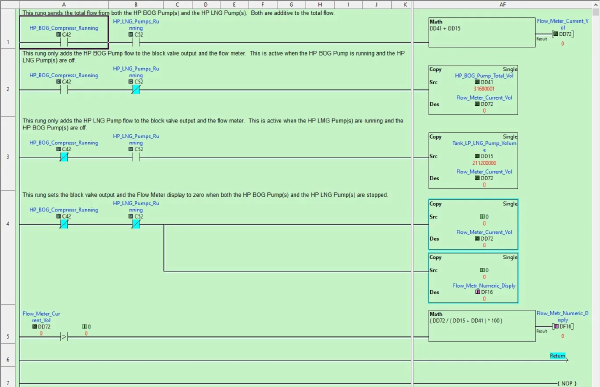
AI Gives Attackers OT Expertise on Demand. Here's What the Technique Looks Like on a Real PLC. (Part 2)